by Alan Blair | Jun 6, 2018 | Article, Cloud Services, Security
Why you need Email Gateway Security. The security industry has provided large businesses with effective email security solutions for many years, helping to address their heightened sensitivity to email risk. Email gateway security solutions have proven particularly... by Alan Blair | May 14, 2018 | Article, Business, Security
Australian business owners need to recognize the importance of data security. IT companies are ready to assist business owners with all their data security needs. With the ever-growing threat of cyber-crime, it becomes more and more important to protect assets before... 
by Alan Blair | May 29, 2017 | Security
This act mandates that all owners and importers of goods must retain records for 5 years and be able to produce records as required. Penalties apply should you not comply. Are your records protected and archived for 5 years? If you are not absolutely certain you must... 
by Alan Blair | May 29, 2017 | Security
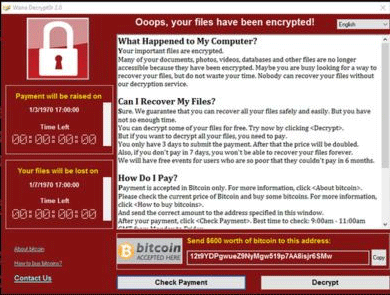
I just found this excellent video on YouTube that I thought I would share with you. It explains very well what Ransom-Ware actually does and how serious a threat it is. The video was published September 2016 but has never been more relevant than today. In the... 
by Alan Blair | May 22, 2017 | Security
We live in a world where everyone seems to believe that nothing bad will ever happen to them so they don’t have to take any steps to prevent the worst. Unfortunately, it is this kind of thinking that can make our job very difficult. Computer security is very important... 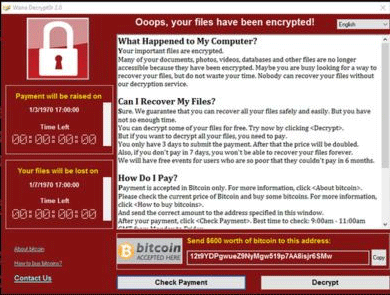
by Alan Blair | May 16, 2017 | Security
WannaCry Ransom-ware – Avast detects over 57,000 users affected More than 70 countries targeted. Major institutions infected, including hospitals. According to experts tracking and analyzing the worm and its spread, this could be one of the worst-ever recorded...



Recent Comments